| Wireles Networking is a practical guide to planning and building low-cost telecommunications infrastructure. See the editorial for more information.... |
|

Home  Security Security  Privacy Privacy  SSH SSH |
|||
| See also: SSL | |||






|
|||
|
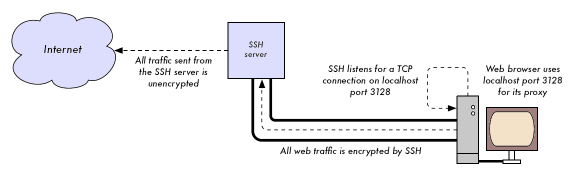
SSHMost people think of SSH as a secure replacement for telnet, just as scp and sftp are the secure counterparts of rcp and ftp. But SSH is much more than encrypted remote shell. Like SSL, it uses strong public key cryptography to verify the remote server and encrypt data. Instead of a PKI, it uses a key fingerprint cache that is checked before a connection is permitted. It can use passwords, public keys, or other methods for user authentication. Many people do not know that SSH can also act as a general purpose encrypting tunnel, or even an encrypting web proxy. By first establishing an SSH connection to a trusted location near (or even on) a remote server, insecure protocols can be protected from eavesdropping and attack. While this technique may be a bit advanced for many users, network architects can use SSH to encrypt traffic across untrusted links, such as wireless point-to-point links. Since the tools are freely available and run over standard TCP, any educated user can implement SSH connections for themselves, providing their own end-to-end encryption without administrator intervention. OpenSSH is probably the most popular implementation on Unix-like platforms. Free implementations such as Putty and WinSCP are available for Windows. OpenSSH will also run on Windows under the Cygwin package. These examples will assume that you are using a recent version of OpenSSH. To establish an encrypted tunnel from a port on the local machine to a port on the remote side, use the -L switch. For example, suppose you want to forward web proxy traffic over an encrypted link to the squid server at squid.example.net. Forward port 3128 (the default proxy port) using this command: ssh -fN -g -L3128:squid.example.net:3128 squid.example.net The -fN switches instruct ssh to fork into the background after connecting. The -g switch allows other users on your local segment to connect to the local machine and use it for encryption over the untrusted link. OpenSSH will use a public key for authentication if you have set one up, or it will prompt you for your password on the remote side. You can then configure your web browser to connect to localhost port 3128 as its web proxy service. All web traffic will then be encrypted before transmission to the remote side.
SSH can also act as a dynamic SOCKS4 or SOCKS5 proxy. This allows you to create an encrypting web proxy, without the need to set up squid. Note that this is not a caching proxy; it simply encrypts all traffic. ssh -fN -D 8080 remote.example.net Configure your web browser to use SOCKS4 or SOCKS5 on local port 8080, and away you go. SSH can encrypt data on any TCP port, including ports used for email. It can even compress the data along the way, which can decrease latency on low capacity links. ssh -fNCg -L110:localhost:110 -L25:localhost:25 mailhost.example.net The -C switch turns on compression. You can add as many port forwarding rules as you like by specifying the -L switch multiple times. Note that in order to bind to a local port less than 1024, you must have root privileges on the local machine. These are just a few examples of the flexibility of SSH. By implementing public keys and using the ssh forwarding agent, you can automate the creation of encrypted tunnels throughout your wireless network, and protect your communications with strong encryption and authentication.
|
|||
Home  Security Security  Privacy Privacy  SSH SSH |
|||
Last Update: 2007-01-24